The one who owns the information owns the power. Reliable information of the high quality allows us to make the right analysis and conclusions no matter what we’re talking about. That’s why people who can get the right information and analyze it are really appreciated at all times. However, sometimes information should be passed so that nobody except for the addressee could know the fact of information transmitting. This is what we call steganography and here we are to reveal some of its secrets.
We offer you firstly an easy problem case that can be helpful for the future experts in the field of information security, especially for those who have problems with their homework in the field as it uses a steganographic method of information protection. So, imagine yourself to be Agent 008. Moreover, you are an art critic in New York. You have an important task from Her Majesty the Queen. You need to urgently convey a simple message to “the Center”. This message can produce a very important political effect. But suddenly your phone was tapped by special secret service. It is not possible to send a message in the letter because you and your agent can be immediately caught and expelled from the country. You are not even able to convey the message to your own agent.
Here comes steganography to help solve this problem as it is exactly he science of secure communication. Unlike cryptography, where the enemy can accurately determine whether a message is an encrypted text, steganographic techniques allow you to embed secret information in the innocuous messages so that it would be impossible to suspect the existence of the embedded secret message. The word “steganography” from Greek literally means secret recording (steganos – a secret, a mystery; graphy – recording). It involves a great many secret means of communication, such as invisible ink, microdots, conditional arrangement of characters, secret channels and means of communication on floating frequencies. Transferring information using steganography is the direction which is actively developing in recent decades and it certainly will evolve in the future. Here you can learn more about this mysterious science:

So, possessing the knowledge of steganography, you decide to draw a picture and put it at the next Biennial in New York. This picture is seen by thousands of visitors, but only one of them will recognize the information hidden there.
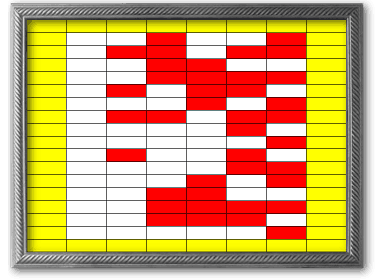
And here’s your picture itself:
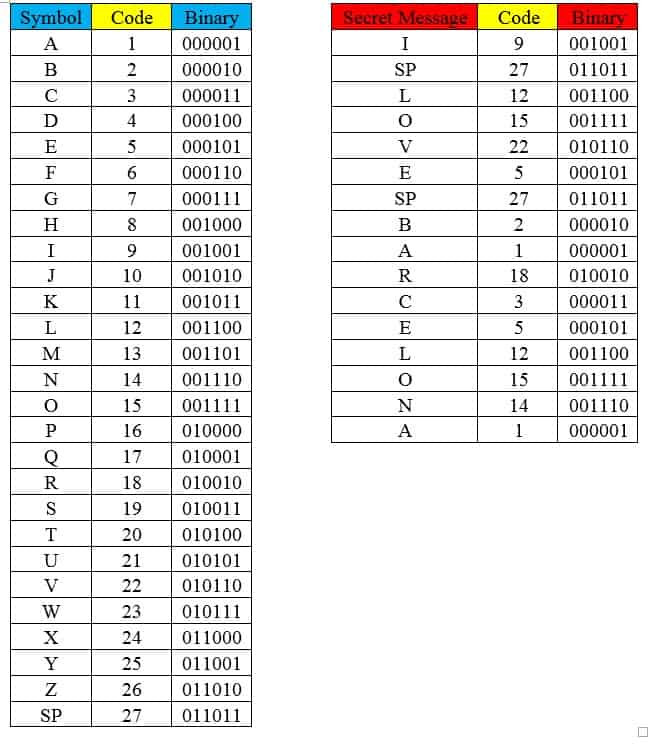
Your hidden message is I LOVE BARCELONA. The message means that it is necessary to change the English ambassador in Spain. Let’s take a closer look at the encoding algorithm. To encode the message using the following spy’s algorithm we have to account that all letters have sequence numbers in the alphabet A-1, B-2, etc. The secret message is made up of letters, where each simply has its own secret message sequence number in the alphabet. The number of each letter in the alphabet is transferred from decimal to binary as it is below.
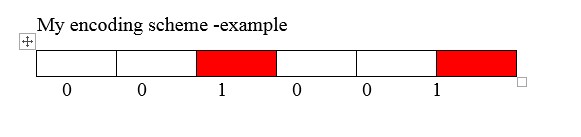
After encrypting it, we get a column of ones and zeros (see binary column). The binary encrypted message is transferred to the canvas, where 1 is the presence of color and 0 is its absence. In this case, ‘0’ is white and “1” is red. The border posts are yellow. The recipient of a secret message takes a photo of your picture and begins the process of decryption. He starts color rendering of images in binary code.
 And after that he transforms the binary code into a decimal code using the following table:
And after that he transforms the binary code into a decimal code using the following table: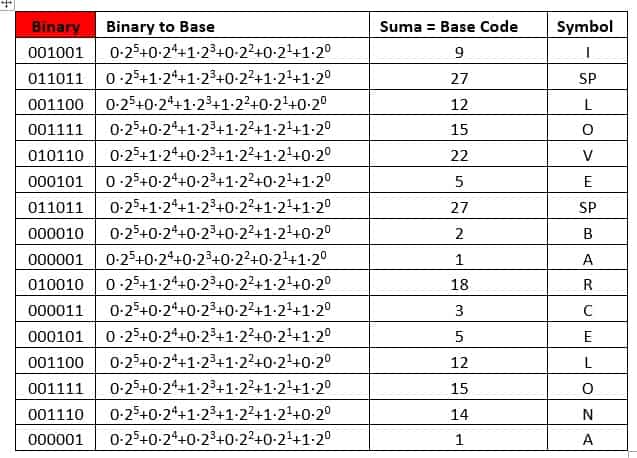
Finally, he finds each decimal to be the letter that corresponds to it. We’ve shown that a seemingly naive painting helps to transmit the right information into the right hands. Now, when you visit any painting exhibition next time, be more attentive to the works art, they may tell you somebody’s secret. However, it still may be way too difficult 🙂